Israeli firm NSO Group has created spyware which can hack a smartphone, beat encryption and access every bit of our data, live-time, just like reading over somebody’s shoulder. Human rights activist and cyber-security expert Manal al Sharif examines the implications. This is the first exclusive in Manal’s Tech4Evil series of investigations which expose the threat of Big Tech on our minds, our humanity and democracy itself.
“They listen to and see everything on your smartphone as if they are next to you. No end-to-end encryption, no privacy settings, no secure connection can stop them. There is nowhere to hide”.
I got this chilling warning from one of my activist friends just as she was released from a Saudi jail back in 2017. As a cybersecurity expert, who is aware of the PRISM program, I know that once you go online, nothing is private anymore. But how could the Saudi government possess such advanced tools to break even encrypted connections?
A year before this incident, I read a report accusing an Israeli company called NSO group of selling advanced surveillance tech to oppressive governments. Such tech is capable of exploiting what’s called “zero-day vulnerabilities” in order to gain access to your smartphone. Zero-day vulnerabilities are flaws which even the maker of the device is unaware of. Exploiting these flaws requires sophisticated reverse engineering and a level of resources which makes it extremely expensive. It is estimated that each zero-day exploit costs at least $US1 million. That is, $US1million to hack just one person’s smartphone.
The surveillance tool is called Pegasus. It is now being sold around the world by Israeli firm NSO Group, and can be installed on your smartphone, sometimes by just getting a missed call, and yes, it works by exploiting a zero-day vulnerability. Once installed, Pegasus then gets full and unconditional access to your phone. That includes your phone calls, encrypted messages, files and images; it can even control your phone remotely by turning the camera and microphone on without your knowledge.
NSO Group insists that it sells its spyware only for the use of national security and counter-terrorism agencies. However, it has been used far more broadly as repressive regimes, activists and journalists are also considered ‘national security threats’. Further, NSO’s claims were later disproved when it was revealed others, outside these groups, had been hacked.
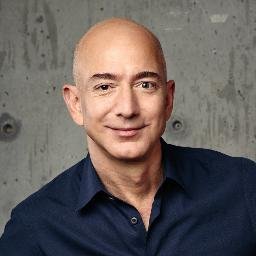
In 2018, there were revelations that Pegasus was suspected of being used to spy on Jeff Bezos’s personal smartphone. Bezos is the founder of Amazon and the world’s richest man. The most likely culprit was none other than Mohammed Bin Salman, or MBS, the Crown Prince of Saudi Arabia, who infected Bezos’ phone by sending a video as a WhatsApp message. The hack was seen as a warning to Bezos, the owner of the Washington Post. The Post had exposed MBS publicly for his possible involvement in the assassination of the its Saudi journalist Jamal Khashoggi. Both Saudi Arabia and NSO Group have denied responsibility.
Throughout 2018 and 2019, I became aware of many cases of hacking against human rights activists in the Arab world. The legal cases against them which followed used private messages which were communicated on encrypted channels. Those activists were arrested and imprisoned, and those who have been released remain subject to travel bans.
I knew their phones must have been hacked using the same sophisticated tools. I personally had to change my phone twice when it started acting weirdly. All those individual cases didn’t gain momentum in public, and were not pursued by enforcement agencies to hold NSO Group accountable for selling Pegasus to repressive governments.
Forbidden Stories
To my astonishment, the silence was finally about to break. Recently, the not-for-profit organisation of investigative journalists, Forbidden Stories, along with human rights group Amnesty International, gained access to a set of more than 50,000 leaked phone numbers believed to be a list of targets of NSO Group’s surveillance tool. This ignited the Pegasus Project, a collaborative effort led by Forbidden Stories and 15 other partners to identify the individuals who owned these numbers and investigate if they were hacked.
The outcome of the preliminary investigation yielded what activists had always feared, that these tools were being deployed to target whomever the hackers identified as a threat.
So far, the investigation has exposed a list of the clients of Pegasus, stretching from Mexico, Hungary, India to the United Arab Emirates and Saudi Arabia; countries with dubious records on human rights and freedom of expression. Out of 1,000 phone numbers whose owners were identified, at least 188 were journalists. Many others were human rights activists, diplomats, politicians, and government officials. At least 10 heads of government were on the list.

Manal al Sharif was jailed for driving a car. It sparked a revolution. Now Saudi women are allowed to drive
Maybe now that some of the identified numbers belong to world leaders, the world will pay attention to the implication of making these highly sophisticated hacking tools available for sale.
NSO Group’s Pegasus is not the first and won’t be the last. Following the Arab Spring, human rights activists and anyone helping them were haunted by the same oppressive governments they were challenging, and not without the help of Western intelligence. The infamous Project Raven, which was funded by the government of the UAE, and targeted not only its citizens but journalists from the US and the UK, would not have been possible without recruiting former US intelligence contractors who brought with them critical experience and expertise.
Bad Karma
The cutting-edge espionage platform they used was known as Karma. “Karma was particularly potent because it did not require a target to click on any link to download malicious software. The operatives understood the hacking tool to rely on an undisclosed vulnerability in Apple’s iMessage text messaging software”, as was reported by Reuters in Jan 2019.
As part of Project Raven, a British journalist, Rori Donaghy, was hacked and all his communications were monitored for three years before Citizen Lab, a Canadian human rights and digital privacy group, helped discover the hack. Donaghy was targeted after publishing stories criticising the Emirati government’s record on human rights.
Before 2012, the Emirati intelligence agency would have to physically break into houses of suspects and tap communication or collect evidence. With Project Raven, their operations could be done remotely and could reach people outside the Emirate’s borders without so much as leaving the comfort of their homes or offices.
For years, UK defence giant BAE Systems has been making lucrative revenue from the sales of sophisticated surveillance technology, including sales to repressive regimes. In 2011, BAE bought Danish cyber and intelligence company ETI and the company became part of BAE Systems Applied Intelligence. Ever since, BAE has used its Danish subsidiary to supply Evident systems to Arab countries such as Morocco, Saudi Arabia, Qatar and the UAE. The BBC followed the story by reporting the findings in 2017 in an investigative documentary, Weapons of Mass Surveillance, which exposed the shady trade of BAE Systems.
“During the course of the BBC investigation, it emerged that sales of Evident could also potentially have an impact on national security in the UK. An upgraded version of the system now offers another capability – decryption or, to use the technical term, cryptanalysis. This enables users to read communications even if they have been security encrypted”, the BBC reported in an alarming tone.
Thanks to BAE Systems, rich and repressive governments today have access to previously unheard-of mass surveillance tools, some of which are able to monitor the communications of an entire nation to look for an individual target by searching their voice print alone. Identifying one person with such precision makes the proverb: “finding a needle in a haystack” an eerie reality.
When I was interviewed for the BBC documentary, I posed my concern: will we ever see a campaign against the mass-surveillance tech industry equivalent to the Campaign Against Arms Trade? Surely it is the moral responsibility of people living in democracies to hold their governments accountable for these dangerous breaches of privacy, and for the sales. Functioning democracies don’t have a price tag on their values once they cross the borders.
_______
Editor’s Note: this is the first in Manal al Sharif’s Tech4Evil series of stories and podcasts which investigates the tech giants Google, Facebook and others and their threat to humanity. It is a rare privilege to publish Manal’s work here at Michael West Media.
The recent Australian media laws (Digital Media Bargaining Code), hailed by our politicians as “historic reforms” do nothing to address the big challenge for regulators around the world, that is, the challenge of regulating surveillance capitalism. With a tweak of their algorithms these global monopolies have the power to change governments, indeed the course of history. Australia’s new laws did nothing more than compelled the tech giants to make payments to the Coalition government’s media allies News Corp, Nine, Seven, and other mainstream media players.
Protection Racket: Digital Media Code a farce as Google and Facebook not “designated”
Manal al-Sharif is an author, speaker, human rights activitist and a regular contributor to international media. She has written for the Time, the NY Times and Washington Post. Her Amazon bestseller memoir, Daring to Drive: a Saudi Woman's Awakening, is an intimate story of her life growing up in one of the most masculine societies in the world.
Manal is a cybersecurity expert and host of the tech4evil.com podcast that discusses the intersection of technology and human rights.